Introduction
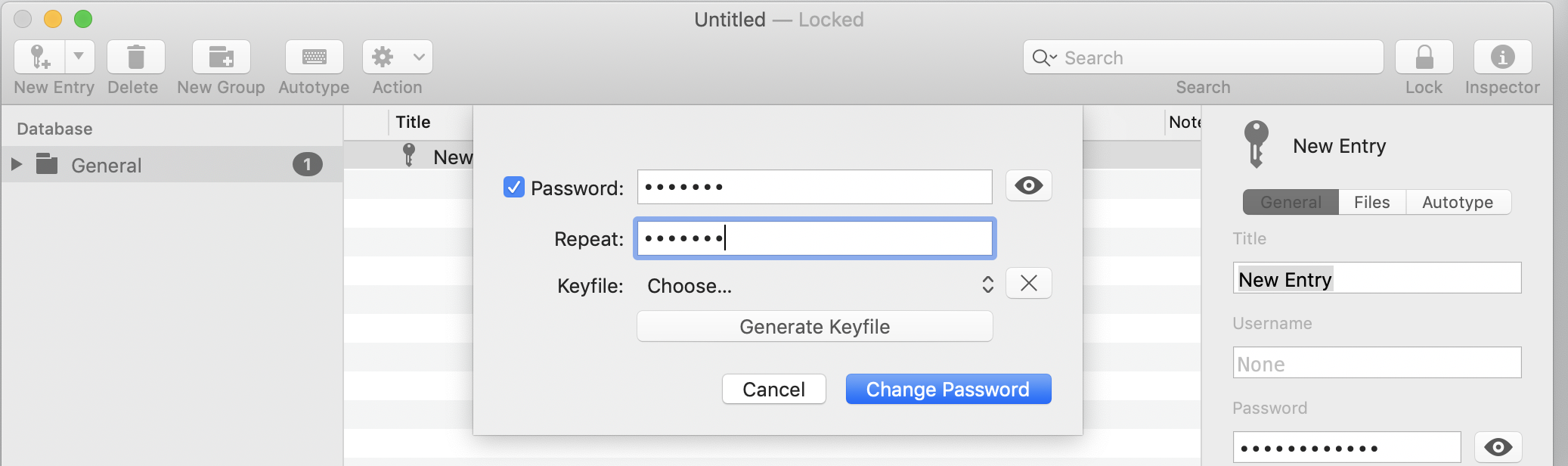
- How To Manage Your Passwords With Macpass Iphone
- How To Manage Your Passwords With Macpass Itunes
- How To Manage Your Passwords With Macpass Chrome
Mac OS X provides screen sharing functionality based VNC and it can be used for remote assistance. This document describes the configuration necessary to enable someone – a colleague or a Service Desk technician – to ask your permission to see your screen and to be to control it remotely in parallel with you.
Enabling someone to ask to see your screen
Step 1 - enable Screen Sharing
To enable the Screen Sharing, open System Preferences and select Sharing. Tick the box for Screen Sharing so that the status becomes 'On'. Then, click on the 'Computer Settings' button on the right.
- Introduction Mac OS X provides screen sharing functionality based VNC and it can be used for remote assistance. This document describes the configuration necessary to enable someone – a colleague or a Service Desk technician – to ask your permission to see your screen and to be to control it remotely in parallel with you.
- For password-management needs that go beyond what Keychain can offer, your best bet is a third-party password manager. Get a high-powered password manager.
- Learn how to fix a forgotten password on your Mac! This will work with any Mac OS X operating system, and will allow you to recover your password for your ac.
Feb 25, 2018 I tried the advice given to other users with the same question, but when I do manage to find my way to credential manager and manage passwords, it demands ID verification with a username and password, which I can't even remember having set up in the first place. I could really use some help with this issue, before I end up in the nut house!
In the pop up window, tick the box for 'Anyone may request permission to control screen'. Validate by clicking on 'OK'.
Step 2 – communicate your hostname or IP address
Once Screen Sharing is on, you will need to communicate your hostname or IP address to the person that you want to share your screen with.

You can do that by reading the text starting with 'vnc://' from the Sharing pane, or by checking your hostname – as registered in CERN network database – using the website at: http://cern.ch/getyourhostname.
Step 3 – accept connection request
When someone tries to connect to your screen, the window 'Share Screen Request' will show up. Click on 'Share Screen' to accept the connection. Please note that the control of your Mac will be shared between you and the person who connects.
Connecting to someone else's screen
In order to connect to someone's screen, open Finder, select Go > Connect to Server and specify the Server address in the form 'vnc://hostname'.
Connectivity and security considerations
Sharing your screen as described above will work only within the local network. It will not work between CERN and a Mac on a different network, for example at home.
Having Screen Sharing enabled can have an impact on the security of your Mac so it is recommended to disable it before you use your Mac on a network other than your work or home network, for example when travelling, in a conference, etc.
How often do you find yourself struggling to come up with new login credentials, only to forget them afterward? Managing passwords for every account, site, and service can certainly get frustrating at times. Even more so, if you consider that the number of internet devices and online accounts in use is constantly growing.
It is essential to make sure each of your passwords is secure. This, in turn, requires that you understand how to manage passwords properly, why it's so important, and what makes a password strong. In this Passwarden® blog post, we'll discuss exactly that!

Why Managing Strong Passwords is Important
Hackers can use a vast array of techniques and tools to gain access to your sensitive information. However, most often a security breach occurs through one of two attack vectors: either via a brute-force attack or by exploiting the victim's negligence of security measures. In both scenarios, the attacker's job is all the easier if the victim uses simple, short, and common passwords.
The dangers of weak passwords
What exactly is wrong with weak passwords? We're going to explore this in the following paragraphs, but for now, here's a bit of password management trivia for you. One of the most commonly used passwords is '123456789', which is by accident also one of the most commonly hacked ones. Think about it.

Of course, we genuinely believe that your password is stronger than that. But if you think about some of the first passwords that come to your mind, upon closer inspection you may find them wanting in terms of strength. Our passwords tend to include at least some of our personalized details - names, birthdays, schools and graduation years, kid and pet names, sports team and favorite band names, etc.
Unfortunately (but not unexpectedly), many of these details are by no means unique enough. Hackers have long been utilizing curated lists of words and phrases that are commonly used in passwords. This allows them to organize global attacks, targeting large groups of people at once. And the most likely first victims of such attacks are users with weak or common passwords.
Passwords and brute-force attacks
One of the most common types of attacks aimed at breaching into user accounts and stealing personal data is aptly named a brute-force attack. In it, a hacker uses a program that attempts to systematically enter every possible combination in an attempt to basically 'guess' your password by trial and error. It might feel like this would take forever, but with a powerful enough computer, and with a weak password, a brute-force attack can crack it in minutes or hours.
Now, it must be noted that no password is totally uncrackable. The only difference between a weak and a strong password is that the latter takes more time to crack. However, this is a vital difference! While a weak password will take a couple of hours to crack, a long, complex, and unique password will take hundreds of years, rendering any attack futile.
3 Rules for Managing Strong Passwords
1. Variety of characters
Creating a strong password is not as difficult as one might think. The first step is to use different types of characters in your password (numbers, special symbols, upper and lowercase letters), which makes it significantly more reliable. By adding even a single character of a different type, you increase the list of potential combinations that an attacker has to try. The more complex the combination of characters - the better.
2. Password length
A healthy mix of characters makes a password more reliable, but making it even a few characters longer increases its security manifold. How long should a password be? The general consensus is - at least 10+ digits long if it combines various types of characters, or at 15+ otherwise. Adding just 3 extra characters to a weak password can increase the time it takes to crack it from hours to centuries.
How To Manage Your Passwords With Macpass Iphone
3. Password uniqueness
Ah, the painful topic of reusing passwords. Most of us know it's a bad habit, and yet we often opt to do reuse a password or two nonetheless. Just to recap, why should you use unique passwords? Because otherwise if a security breach reveals a password on one of your accounts, it automatically jeopardizes all the others where you use the same password. And coincidentally, the first thing a hacker does when they get their hands on your password is to try it on every other account and email that belongs to you.

You can do that by reading the text starting with 'vnc://' from the Sharing pane, or by checking your hostname – as registered in CERN network database – using the website at: http://cern.ch/getyourhostname.
Step 3 – accept connection request
When someone tries to connect to your screen, the window 'Share Screen Request' will show up. Click on 'Share Screen' to accept the connection. Please note that the control of your Mac will be shared between you and the person who connects.
Connecting to someone else's screen
In order to connect to someone's screen, open Finder, select Go > Connect to Server and specify the Server address in the form 'vnc://hostname'.
Connectivity and security considerations
Sharing your screen as described above will work only within the local network. It will not work between CERN and a Mac on a different network, for example at home.
Having Screen Sharing enabled can have an impact on the security of your Mac so it is recommended to disable it before you use your Mac on a network other than your work or home network, for example when travelling, in a conference, etc.
How often do you find yourself struggling to come up with new login credentials, only to forget them afterward? Managing passwords for every account, site, and service can certainly get frustrating at times. Even more so, if you consider that the number of internet devices and online accounts in use is constantly growing.
It is essential to make sure each of your passwords is secure. This, in turn, requires that you understand how to manage passwords properly, why it's so important, and what makes a password strong. In this Passwarden® blog post, we'll discuss exactly that!
Why Managing Strong Passwords is Important
Hackers can use a vast array of techniques and tools to gain access to your sensitive information. However, most often a security breach occurs through one of two attack vectors: either via a brute-force attack or by exploiting the victim's negligence of security measures. In both scenarios, the attacker's job is all the easier if the victim uses simple, short, and common passwords.
The dangers of weak passwords
What exactly is wrong with weak passwords? We're going to explore this in the following paragraphs, but for now, here's a bit of password management trivia for you. One of the most commonly used passwords is '123456789', which is by accident also one of the most commonly hacked ones. Think about it.
Jul 27, 2018 - When you purchase a Cisco router, it comes with an IOS image that has all feature sets included in it but you need to activate it with the help of license. Cisco IOS 15 comes with 4 Feature sets and these 4 Features set combined into one single IOS image called as the universal image. Licensing and Cisco Licensing Manager You should note that IOS 15 enforces licensing for the Advanced feature sets. That is, you will need to register a license key for every IOS image that needs Advanced IP and receive an activation key to activate those features. Licensing is basically similar to how the ASA software licenses work today. Understating Cisco IOS v15 Licenses. Prior to IOS 15, we used to have 8 IOS images Types (Feature set), by the way it was 12 before it comes 8. Any router was coming with IB Base feature set and according to your company needs you can go for advance feature set and replace the IOS, check the below pic.
Of course, we genuinely believe that your password is stronger than that. But if you think about some of the first passwords that come to your mind, upon closer inspection you may find them wanting in terms of strength. Our passwords tend to include at least some of our personalized details - names, birthdays, schools and graduation years, kid and pet names, sports team and favorite band names, etc.
Unfortunately (but not unexpectedly), many of these details are by no means unique enough. Hackers have long been utilizing curated lists of words and phrases that are commonly used in passwords. This allows them to organize global attacks, targeting large groups of people at once. And the most likely first victims of such attacks are users with weak or common passwords.
Passwords and brute-force attacks
One of the most common types of attacks aimed at breaching into user accounts and stealing personal data is aptly named a brute-force attack. In it, a hacker uses a program that attempts to systematically enter every possible combination in an attempt to basically 'guess' your password by trial and error. It might feel like this would take forever, but with a powerful enough computer, and with a weak password, a brute-force attack can crack it in minutes or hours.
Now, it must be noted that no password is totally uncrackable. The only difference between a weak and a strong password is that the latter takes more time to crack. However, this is a vital difference! While a weak password will take a couple of hours to crack, a long, complex, and unique password will take hundreds of years, rendering any attack futile.
3 Rules for Managing Strong Passwords
1. Variety of characters
Creating a strong password is not as difficult as one might think. The first step is to use different types of characters in your password (numbers, special symbols, upper and lowercase letters), which makes it significantly more reliable. By adding even a single character of a different type, you increase the list of potential combinations that an attacker has to try. The more complex the combination of characters - the better.
2. Password length
A healthy mix of characters makes a password more reliable, but making it even a few characters longer increases its security manifold. How long should a password be? The general consensus is - at least 10+ digits long if it combines various types of characters, or at 15+ otherwise. Adding just 3 extra characters to a weak password can increase the time it takes to crack it from hours to centuries.
How To Manage Your Passwords With Macpass Iphone
3. Password uniqueness
Ah, the painful topic of reusing passwords. Most of us know it's a bad habit, and yet we often opt to do reuse a password or two nonetheless. Just to recap, why should you use unique passwords? Because otherwise if a security breach reveals a password on one of your accounts, it automatically jeopardizes all the others where you use the same password. And coincidentally, the first thing a hacker does when they get their hands on your password is to try it on every other account and email that belongs to you.
Using a Password Manager for Strong Passwords
To sum up the above, a strong password should be long enough, contain a variety of types of characters, and be unique. Here's a random example of a strong password, generated in Passwarden: F*j9upoFj)7f2agkvz. Now imagine you have something similar for a password per each of your accounts. This raises a valid question: how are you supposed to remember all those? Well, you aren't - a password manager should do it for you!
A cloud-based password manager like Passwarden is a helpful tool that allows you to:
- Securely store your passwords, along with other sensitive information (logins, ID card, Driver's License, SSN, credit cards and banking information, etc.)
- Conveniently manage and easily retrieve the stored data when needed (password autofill option included)
- Add extra layers of security with Two-Factor Authentication and Duress Mode
- Generate strong passwords and instantly save them in protected vaults
- Safely share your passwords and data with others
- Ensure the privacy of your information thanks to the zero-knowledge architecture
Read more:How do password managers work?
How to Manage Passwords With Passwarden
Using a dedicated app to manage passwords comes with its pros and cons. However, anyone who's concerned about the security of their passwords and data would do well to use a password manager. As opposed to other, less reliable means, e.g. writing passwords down on sticky notes or digital sheets.
How To Manage Your Passwords With Macpass Itunes
How to start using Passwarden
Our password manager is really easy to take up! You can download and use it or free right now using the free subscription. You can also check out Passwarden paid subscriptions for more advanced options.
Once you sign in with a new or existing KeepSolid ID, you will be prompted to create a Master Password. This is a very important step! Master Password is your key to Passwarden, which means two things:
- You want to make sure that it's well-protected - strong enough to withstand a brute-force attack, and reinforced with two-factor authentication
- You don't want to lose it - without it, not even Passwarden's employees can access your data (see how to recover your Master Password)
With your newly created Master Password, you'll be able to access your Passwarden account and start managing your passwords and sensitive information in Vaults. A Vault is a single, separate storage place. You can create any number of Vaults for different purposes (e.g. a personal Vault for your own data and a shared Vault for your family account passwords).
How to manage saved passwords
What if you wanted to use Passwarden to manage passwords that you already have stored in other apps, for example in a browser? In this case, you could utilize the Data Migration feature. It allows you to import passwords from different apps directly to Passwarden. This is a very convenient option since otherwise, you'd have to manually transfer what could easily be thousands of passwords!
How To Manage Your Passwords With Macpass Chrome
How to manage passwords on Mac, iPhone, Chrome, Safari, and other devices
With Passwarden, you can manage passwords on all popular platforms, including macOS, iOS, Windows, Android, browsers, and using the web app. Moreover, you can use Passwarden on any number of devices simultaneously. And with the cloud-based data synchronization, any passwords that you save on one of your devices will instantly become available on all the others where you're signed in to your Passwarden account.
