Cisco IOS 15 License Eval. Posted by 5 years ago. Cisco IOS 15 License Eval. Hello, we have a Cisco 1921 router in a lab environment that we do a lot of our mock up configurations on. I just experienced the process of upgrading the router to the 'DataK9' package by following a walkthrough that I found on Google.
- Cisco Ios Download
- Cisco Ios 15 License Keygen Key Generator
- Cisco Ios 15 License Keygen 2016
- Cisco Ios 15 License Keygen Update
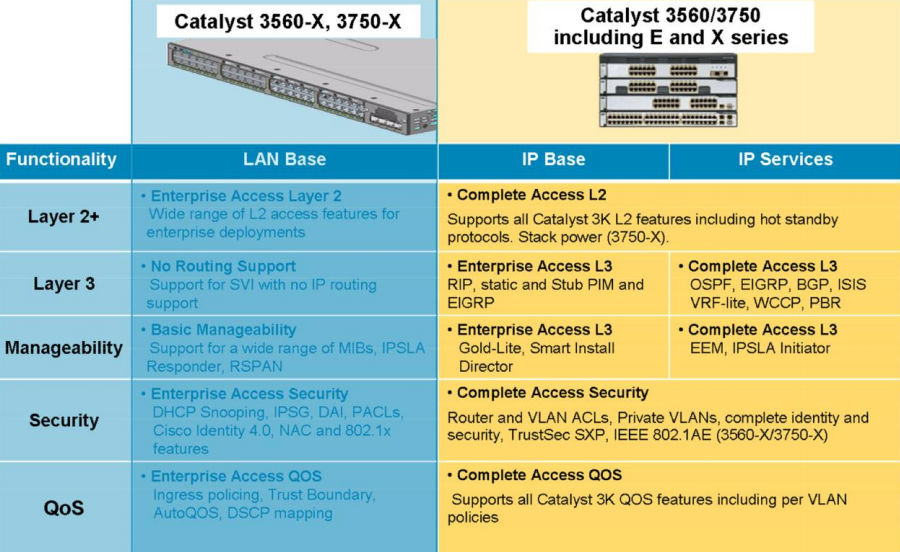
You can find Cisco serial numbers from the IOS command line by using the show inventory command. This is good news for all the folks out there that have needed to collect this information remotely for service contracts, TAC cases, etc. Jan 21, 2014 Understating Cisco IOS v15 Licenses 1. Understating Cisco IOS v15 Licenses Prior to IOS 15, we used to have 8 IOS images Types (Feature set), by the way it was 12 before it comes 8. Any router was coming with IB Base feature set and according to your company needs you can go for advance feature set and replace the IOS, check the below pic: The following Picture explain each one and what. Use the Cisco Software Checker to search for Cisco Security Advisories that apply to specific Cisco IOS, IOS XE, NX-OS and NX-OS in ACI Mode software releases. To use the tool, select a product and choose one or more releases from the drop-down list, enter the output of the show version command, or upload a text file that lists specific. Jul 27, 2018 - When you purchase a Cisco router, it comes with an IOS image that has all feature sets included in it but you need to activate it with the help of license. Cisco IOS 15 comes with 4 Feature sets and these 4 Features set combined into one single IOS image called as the universal image.
Configure a certificate compatible with Cisco IOS by XCA on Ubuntu.
- Export a CA certificate in PEM-encoding on XCA:
Click an image to zoom in.
Open the saved certificate file (TestCA.crt) by text editor.
-----BEGIN CERTIFICATE----- MIIDUjCCAjqgAwIBAgIBATANBgkqhkiG9w0BAQUFADBNMQswCQYDVQQGEwJKUDEO MAwGA1UECBMFVG9reW8xEDAOBgNVBAoTB2V4YW1wbGUxHDAaBgNVBAMTE2Npc2Nv .... aEXQ/TpHN3IQ5DwOakXFdbNgP1uP8IhvDLB7wnPY1cJpIFU4CB0= -----END CERTIFICATE----- |
- Generate RSA keys and create a Certificate Signing Request (CSR) on Cisco IOS (cisco1.example.com)
Cisco Ios Download
See Command References for Cisco IOS 15.1M&T for more details.router(config)# show version .... Cisco IOS Software, 1841 Software (C1841-ADVSECURITYK9-M), Version 15.1(4)M8, RELEASE SOFTWARE (fc2) .... Cisco 1841 (revision 7.0) with 239616K/22528K bytes of memory. .... |
router(config)# hostname cisco1 cisco1(config)# ip domain example.com |
cisco1(config)# crypto key generate rsa modulus 2048 general-keys The key modulus size is 2048 bits Generating 2048 bit RSA keys, keys will be non-exportable...[OK] |
cisco1(config)# crypto pki trustpoint ciscoca cisco1(ca-trustpoint)# enrollment terminal cisco1(ca-trustpoint)# fqdn none cisco1(ca-trustpoint)# ip-address none cisco1(ca-trustpoint)# subject-name CN=cisco1.example.com,O=example,ST=Tokyo,C=JP cisco1(ca-trustpoint)# rsakeypair cisco1.example.com cisco1(ca-trustpoint)# revocation-check none cisco1(ca-trustpoint)# exit |
cisco1(config)# crypto pki authenticate ciscoca Enter the base 64 encoded CA certificate. End with a blank line or the word 'quit' on a line by itself (Paste the PEM-encoded contents of above TestCA.crt. The PEM header and footer are not included.) MIIDUjCCAjqgAwIBAgIBATANBgkqhkiG9w0BAQUFADBNMQswCQYDVQQGEwJKUDEO MAwGA1UECBMFVG9reW8xEDAOBgNVBAoTB2V4YW1wbGUxHDAaBgNVBAMTE2Npc2Nv .... aEXQ/TpHN3IQ5DwOakXFdbNgP1uP8IhvDLB7wnPY1cJpIFU4CB0= Do you accept this certificate? [yes/no]: yes Trustpoint CA certificate accepted. Certificate successfully imported cisco1(config)# exit cisco1# show crypto pki certificates ... CA Certificate Status: Available Certificate Serial Number (hex): 01 Certificate Usage: General Purpose Issuer: cn=testca.example.com o=example st=Tokyo c=JP Subject: cn=testca.example.com o=example st=Tokyo c=JP Validity Date: start date: xxxx end date: xxxx Associated Trustpoints: ciscoca Storage: nvram:ciscocaexamp#1CA.cer |
cisco1(config)# crypto pki enroll ciscoca Start certificate enrollment .. .... Include the router serial number in the subject name? [yes/no]: no .... Display Certificate Request to terminal? [yes/no]: yes Certificate Request follows: MIICsjCCAZoCAQAwTDELMAkGA1UEBhMCSlAxDjAMBgNVBAgTBVRva3lvMRAwDgYD VQQKEwdleGFtcGxlMRswGQYDVQQDExJjaXNjbzEuZXhhbXBsZS5jb20wggEiMA0G .... KKdrWOkisCNsOfivsOPXoA5Cw53aVQ |
Copy the displayed Certificate Request (CSR) contents (PEM), paste into a file by text editor and then save it as cisco1.example.com.csr.
Click an image to zoom in.
- Export a CA certificate in PEM-encoding on XCA:
Click an image to zoom in.
Open the saved certificate file (TestCA.crt) by text editor.
-----BEGIN CERTIFICATE----- MIIDUjCCAjqgAwIBAgIBATANBgkqhkiG9w0BAQUFADBNMQswCQYDVQQGEwJKUDEO MAwGA1UECBMFVG9reW8xEDAOBgNVBAoTB2V4YW1wbGUxHDAaBgNVBAMTE2Npc2Nv .... aEXQ/TpHN3IQ5DwOakXFdbNgP1uP8IhvDLB7wnPY1cJpIFU4CB0= -----END CERTIFICATE----- |
- Generate RSA keys and create a Certificate Signing Request (CSR) on Cisco IOS (cisco1.example.com)
Cisco Ios Download
See Command References for Cisco IOS 15.1M&T for more details.router(config)# show version .... Cisco IOS Software, 1841 Software (C1841-ADVSECURITYK9-M), Version 15.1(4)M8, RELEASE SOFTWARE (fc2) .... Cisco 1841 (revision 7.0) with 239616K/22528K bytes of memory. .... |
router(config)# hostname cisco1 cisco1(config)# ip domain example.com |
cisco1(config)# crypto key generate rsa modulus 2048 general-keys The key modulus size is 2048 bits Generating 2048 bit RSA keys, keys will be non-exportable...[OK] |
cisco1(config)# crypto pki trustpoint ciscoca cisco1(ca-trustpoint)# enrollment terminal cisco1(ca-trustpoint)# fqdn none cisco1(ca-trustpoint)# ip-address none cisco1(ca-trustpoint)# subject-name CN=cisco1.example.com,O=example,ST=Tokyo,C=JP cisco1(ca-trustpoint)# rsakeypair cisco1.example.com cisco1(ca-trustpoint)# revocation-check none cisco1(ca-trustpoint)# exit |
cisco1(config)# crypto pki authenticate ciscoca Enter the base 64 encoded CA certificate. End with a blank line or the word 'quit' on a line by itself (Paste the PEM-encoded contents of above TestCA.crt. The PEM header and footer are not included.) MIIDUjCCAjqgAwIBAgIBATANBgkqhkiG9w0BAQUFADBNMQswCQYDVQQGEwJKUDEO MAwGA1UECBMFVG9reW8xEDAOBgNVBAoTB2V4YW1wbGUxHDAaBgNVBAMTE2Npc2Nv .... aEXQ/TpHN3IQ5DwOakXFdbNgP1uP8IhvDLB7wnPY1cJpIFU4CB0= Do you accept this certificate? [yes/no]: yes Trustpoint CA certificate accepted. Certificate successfully imported cisco1(config)# exit cisco1# show crypto pki certificates ... CA Certificate Status: Available Certificate Serial Number (hex): 01 Certificate Usage: General Purpose Issuer: cn=testca.example.com o=example st=Tokyo c=JP Subject: cn=testca.example.com o=example st=Tokyo c=JP Validity Date: start date: xxxx end date: xxxx Associated Trustpoints: ciscoca Storage: nvram:ciscocaexamp#1CA.cer |
cisco1(config)# crypto pki enroll ciscoca Start certificate enrollment .. .... Include the router serial number in the subject name? [yes/no]: no .... Display Certificate Request to terminal? [yes/no]: yes Certificate Request follows: MIICsjCCAZoCAQAwTDELMAkGA1UEBhMCSlAxDjAMBgNVBAgTBVRva3lvMRAwDgYD VQQKEwdleGFtcGxlMRswGQYDVQQDExJjaXNjbzEuZXhhbXBsZS5jb20wggEiMA0G .... KKdrWOkisCNsOfivsOPXoA5Cw53aVQ |
Copy the displayed Certificate Request (CSR) contents (PEM), paste into a file by text editor and then save it as cisco1.example.com.csr.
Click an image to zoom in.
Before saving the file, you need to add the PEM header and footer like this:
-----BEGIN CERTIFICATE REQUEST----- MIICsjCCAZoCAQAwTDELMAkGA1UEBhMCSlAxDjAMBgNVBAgTBVRva3lvMRAwDgYD
VQQKEwdleGFtcGxlMRswGQYDVQQDExJjaXNjbzEuZXhhbXBsZS5jb20wggEiMA0G
....
KKdrWOkisCNsOfivsOPXoA5Cw53aVQ
-----END CERTIFICATE REQUEST-----
Cisco Ios 15 License Keygen Key Generator
- Sign and export a new certificate for cisco1.example.com by XCA:
- Import the Certificate Signing Request (CSR) for cisco1.example.com.
- Sign a certificate for cisco1.example.com by TestCA.
- Export the certificate to a PEM file.
- File name: cisco1.example.com.crt - Open the signed certificate file (cisco1.example.com.crt) by text editor and copy the contents without the PEM header and footer.
Click an image to zoom in.
Click an image to zoom in.
Click an image to zoom in.
- Import the signed certificate into Cisco IOS (cisco1.example.com)
Cisco Ios 15 License Keygen 2016
Cisco Ios 15 License Keygen Update
cisco1(config)# crypto pki import ciscoca certificate Enter the base 64 encoded certificate. End with a blank line or the word 'quit' on a line by itself (Paste the certificate contents copied from the text editor above.) MIIDTzCCAjegAwIBAgIBAjANBgkqhkiG9w0BAQUFADBMMQswCQYDVQQGEwJKUDEO MAwGA1UECBMFVG9reW8xEDAOBgNVBAoTB2V4YW1wbGUxGzAZBgNVBAMTEnRlc3Rj .... pS/8x8Azvi9uXDp/Uv8FX5WtgmctUAqYlHogq9FN/PsSKNU= Router Certificate successfully imported |
cisco1# show crypto pki certificates Certificate Status: Available Certificate Serial Number (hex): 03 Certificate Usage: General Purpose Issuer: cn=testca.example.com o=example st=Tokyo c=JP Subject: Name: cisco1.example.com cn=cisco1.example.com o=example st=Tokyo c=JP Validity Date: start date: xxxxxx end date: xxxxxx Associated Trustpoints: ciscoca Storage: nvram:ciscocaexamp#2.cer CA Certificate Status: Available Certificate Serial Number (hex): 01 Certificate Usage: General Purpose Issuer: cn=ciscoca.example.com o=example st=Tokyo c=JP Subject: cn=ciscoca.example.com o=example st=Tokyo c=JP Validity Date: start date: xxxxxx end date: xxxxxx Associated Trustpoints: ciscoca Storage: nvram:ciscocaexamp#1CA.cer cisco1# show crypto pki trustpoints status Trustpoint ciscoca: Issuing CA certificate configured: Subject Name: cn=testca.example.com,o=example,st=Tokyo,c=JP Fingerprint MD5: xxxxxx AE222650 xxxxxx 3CE7EFFC Fingerprint SHA1: xxxxxx 88837420 xxxxxx 55B0EC8E xxxxxx Router General Purpose certificate configured: Subject Name: cn=cisco1.example.com,o=example,st=Tokyo,c=JP Fingerprint MD5: xxxxxx 1DC1EACB xxxxxx 8C16CA3E Fingerprint SHA1: xxxxxx 3C2DBF77 xxxxxx D35604A3 xxxxxx State: Keys generated ............. Yes (General Purpose, non-exportable) Issuing CA authenticated ....... Yes Certificate request(s) ..... Yes |
